Phone: +1 201 488 1022
Fax: +1 201 488 1244
Markets
Safeguards’ systems are installed in Correctional Institutions, United States Department of Defense Facilities, Department of Energy Sites, Nuclear Power Generating Stations and Civilian Airports throughout the United States.
To further break-down Safeguards Technology’s customer base into something more facility-specific, the following has been compiled using the Department of Homeland Security’s (DHS) National Infrastructure Protection Plan Sector Specific Agency and HSPD-7 Assigned Critical Infrastructure/Key Resources Sectors. In the changing realities of today’s world, the DHS has assumed ownership of the security of our nation’s resources and has been granted “rule-setting” authority over what will be done at each facility concerning today’s threats. Since the creation of the DHS, Safeguards has been working diligently within the “new rules of engagement” set down by DHS.
Energy
Persons wishing to attack a nuclear reactor or other nuclear facility have a wide range of options. They may seek to intercept or sabotage shipments of fuel or waste; invade a facility using armed force or deception, then proceed to steal radioactive material, blow up the facility, or (if it is a reactor) cause it to melt down; or seek to breach the containments of reactors or waste-storage facilities using truck bombs, missiles, hijacked aircraft, or other means. All facilities containing significant amounts of radioactive material must therefore be defended from a wide range of possible attacks.
Reactor and waste-storage security has been based on a concept known as "defense-in-depth." The defense-in-depth method requires that each nuclear facility be surrounded by concentric security barriers. The outermost barrier must be an array of fencing and razor wire strategically designed to delay and entrap intruders. The grounds near the fence, inside and out, are monitored by intrusion detection devices, and vehicles can only enter through checkpoints staffed by armed guards. Vehicle and pedestrian access is strictly controlled.
Safeguards Technology, LLC has successfully completed defense-in-depth projects at over 25 nuclear and energy producing facilities in the United States and Canada.


Corrections
In today’s world of growing inmate populations, it has never been more important to ensure that each facility selects and maintains the most suitable and effective perimeter security solution. Unique circumstances and specific needs of each facility must be addressed in order to provide the facility with the security it requires. Ensuring flawless design, engineering, and installation of a perimeter security system are all a part of our commitment to security and dedication to our customers.
Over the past 25 years, Safeguards Technology has provided security solutions to over 90 correctional facilities belonging to the federal government, state governments, and municipalities. Our solutions have included turnkey
installations where the concepts of “deter, detect, and delay” have been strategically addressed using the most advanced intrusion detection technology and physical delay systems.

Transportation
Protecting critical airport infrastructure has led to increased budget allocations to combat security threats and protect airport perimeters. A proactive approach is being taken to install integrated security solutions that will be interoperable with new, emerging technologies, as well as legacy security systems.
Railway, mass transit, and trucking facilities also have inherent characteristics that make them susceptible and vulnerable to potential attacks. From barrier solutions like bollards and fencing to analytical video and access control, Safeguards Technology can provide an integrated solution to protect your vital assets.
Seaports are also crucial gateways for the movement of international commerce and are vital to the economic success of our country. Ships that ply the maritime domain are the primary mode of transportation for world trade, carrying more than 80 percent of the world’s trade by volume. Vessels, containers, cargo, and commercial vehicles are also potential media for smuggling and infiltration of weapons and perpetrators, as well as potential conveyances of devices for direct attacks on port complexes

Department of Defense
Facilities belonging to any of our military branches world-wide, offer our enemies significant targets for both real and political victories. Inflicting even the smallest amount of damage on the organized military forces of the United States is viewed as a victory in certain parts of the world. Because of this fact, military assets must present superior physical obstacles against hostile actions. Throwing large numbers of personnel at the problem is not feasible in the long term. Technology provides a better and, going forward, a more cost-efficient means of protecting our military assets. Perimeter security for these assets will continue to rely on the defense-in-depth philosophy (previously discussed under the nuclear heading) in which concentric security barriers and buffer zones both aid detection of a breach and delay an attack. This allows time for a sufficiently equipped response force to react to the threat. The most effective and reliable intrusion detection systems use multiple technologies to increase the probability of early detection under a broad range of conditions.

Homeland Security
To further break-down Safeguards Technology’s customer base into something more facility-specific, the following has been compiled using the Department of Homeland Security’s (DHS) National Infrastructure Protection Plan Sector Specific Agency and HSPD-7 Assigned Critical Infrastructure/Key Resources Sectors. In the changing realities of today’s world, the DHS has assumed ownership of the security of our nation’s resources and has been granted “rule-setting” authority over what will be done at each facility concerning today’s threats. Since the creation of the DHS, Safeguards has been working diligently within the “new rules of engagement” set down by DHS.
Critical Assets
The terrorism protection capability of data centers, financial institutions, and pharmaceutical facilities, and to another degree, museums and historical sites are currently, and justifiably, undergoing major upgrades. Previously considered "soft targets" by extremists, such facilities provide a wide range of critical functionality to our culture and would represent a major “moral victory to the followers of these extremists if they were successfully damaged or destroyed. Vulnerability assessments for facilities of this type invariably recommend perimeter security relying on the defense-in-depth philosophy in which concentric security barriers and buffer zones both aid detection of a breach and delay an attack. This allows time for a sufficiently equipped response force to react to the threat.

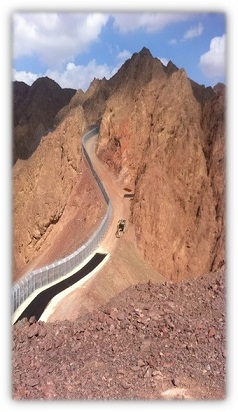
Borders
Border Protection prevents people from entering countries illegally, or transporting anything harmful or illegal between countries .
Boarder protection is important to keep the peace between neighboring countries, whether they are friendly or have sensitive diplomatic relationships.